Fisrt Part -> What should we know about AWS Security? (Part 1)
Mitigation Techniques to DDOS attacks
Some forms of DDoS mitigation are included automatically with AWS services. You can further improve your DDoS resilience by using an AWS architecture with specific services and by implementing additional best practices.
Benefits of using Amazon CloudFront and Amazon Route 53 include the following:
- AWS Shield DDoS mitigation systems that are integrated with AWS edge services, reducing time-to-mitigate from minutes to sub-second.
- Stateless SYN Flood mitigation techniques that proxy and verify incoming connections before passing them to the protected service.
- Automatic traffic engineering systems that can disperse or isolate the impact of large volumetric DDoS attacks.
- Application layer defense when combined with AWS WAF that does not require changing your current application architecture (for example, in an AWS Region or on-premises datacenter).
DDoS-resilient Reference Architecture
AWS Shield Advanced, you get the following additional benefits:
- Access to the AWS DDoS Response Team (DRT) for assistance in mitigating DDoS attacks that impact application availability.
- DDoS attack visibility by using the AWS Management Console, API, and Amazon CloudWatch metrics and alarms.
- Access to the Global Threat Environment dashboard, which provides an overview of DDoS attacks observed and mitigated by AWS.
- Access to AWS WAF, at no additional cost, for the mitigation of application layer DDoS attacks (when used with Amazon CloudFront or ALB).
- Automatic baselining of web traffic attributes, when used with AWS WAF.
- Access to AWS Firewall Manager, at no additional cost, for automated policy enforcement. This service lets security administrators centrally control and manage AWS WAF rules.
- Sensitive detection thresholds which routes traffic into DDoS mitigation system earlier and can improve time-to-mitigate attacks against Amazon EC2 or NLB, when used with EIP.
- Cost protection that allows you to request a limited refund of scaling- related costs that result from a DDoS attack.
- Enhanced service level agreement that is specific to AWS Shield Advanced customers.
Infrastructure Layer Defense (BP1, BP3, BP6, BP7)
Key considerations to help mitigate volumetric DDoS attacks include ensuring that enough transit capacity and diversity is available, and protecting your AWS resources, like Amazon EC2 instances, against attack traffic.
Instance Size (BP7)
Amazon EC2 provides resizable compute capacity so that you can quickly scale up or down as your requirements change.
Choice of Region (BP7)
AWS services are available in multiple locations worldwide.
Load Balancing (BP6)
Large DDoS attacks can overwhelm the capacity of a single Amazon EC2 instance, so adding load balancing can help your resiliency.
Deliver at Scale Using AWS Edge Locations (BP1, BP3)
Access to highly-scaled, diverse internet connections can significantly increase your ability to optimize latency and throughput to users, to absorb DDoS attacks, and to isolate faults while minimizing the impact on your application’s availability
Web Application Delivery at the Edge (BP1)
Amazon CloudFront is a service that can be used to deliver your entire website, including static, dynamic, streaming, and interactive content
Domain Name Resolution at the Edge (BP3)
Amazon Route 53 is a highly available and scalable domain name system (DNS) service that can be used to direct traffic to your web application
When you use Amazon CloudFront and AWS WAF with Amazon API Gateway, configure the following options:
- Configure the cache behavior for your distributions to forward all headers to the API Gateway regional endpoint. By doing this, CloudFront will treat the content as dynamic and skip caching the content.
- Protect your API Gateway against direct access by configuring the distribution to include the origin custom header x-api-key, by setting the API key value in API Gateway.
- Protect your backend from excess traffic by configuring standard or burst rate limits for each method in your REST APIs.
Amazon CloudWatch metrics that are commonly used to detect and react to DDoS attacks
AWS Credentials (Credential types and uses)
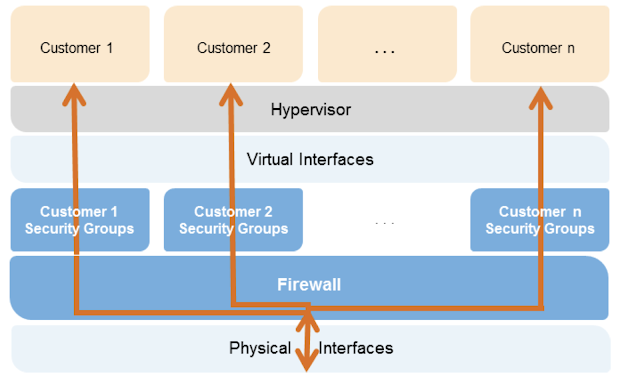
Amazon EC2 multiple layers of security
Types of access control
Amazon DynamoDB Security ( Database-level permissions)
Design Principles
In the cloud, there are a number of principles that can help you strengthen your system security:
- Implement a strong identity foundation:Implement the principle of least privilege and enforce separation of duties with appropriate authorization for each interaction with your AWS resources.
- Enable traceability: Monitor, alert, and audit actions and changes to your environment in real time.
- Apply security at all layers:Rather than just focusing on protection of a single outer layer, apply a defense-in-depth approach with other security controls. Apply to all layers (e.g., edge network, VPC, subnet, load balancer, every instance, operating system, and application).
- Automate security best practices: Automated software-based security mechanisms improve your ability to securely scale more rapidly and cost effectively.
- Protect data in transit and at rest:Classify your data into sensitivity levels and use mechanisms, such as encryption, tokenization, and access control where appropriate.
- Keep people away from data: Create mechanisms and tools to reduce or eliminate the need for direct access or manual processing of data.
- Prepare for security events:Prepare for an incident by having an incident management process that aligns to your organizational requirements.
Security in the cloud is composed of five areas:
- Identity and access management
- Detective controls
- Infrastructure protection
- Data protection
- Incident response
Protecting AWS Credentials
The key AWS service that supports capturing key activities is CloudTrail, which provides rich detail about API calls made in your AWS account. The following services and features are also important:
- Amazon GuardDuty is a managed threat detection service that continuously monitors for malicious or unauthorized behavior to help you protect your AWS accounts and workloads.
- AWS Config provides you with an AWS resource inventory, configuration history, and configuration change notifications to enable security and governance.
- Amazon CloudWatch Logs allows you to centralize logs into streams, natively integrating with features and services like Amazon VPC Flow Logs and CloudTrail.
- Amazon Simple Storage Service (S3) and Amazon Glacier can be used to centralize storage and long-term archiving of log data.
- Amazon Athena can be used to analyze logs, such as CloudTrail logs, to help you identify trends and further isolate activity by attribute, such as source IP address or user.
Integrate Auditing Controls with Notification and Workflow
The following services and features are also important:
- AWS Config Rules enables you to create rules that automatically check the configuration of AWS resources recorded by AWS Config.
- Amazon CloudWatch and CloudWatch Logs must be enabled to facilitate collection of events and routing with CloudWatch Events.
- Amazon CloudWatch API and AWS SDKs can be used to create custom events in your own applications and inject them into CloudWatch Events for rule-based processing and routing.
- Amazon Inspector offers a programmatic way to find security defects or misconfigurations in your operating systems and applications.
Protecting Network and Host-Level Boundaries
The key AWS service that supports the protection of network- and host-level boundaries is Amazon VPC. This service gives you the ability to create your private virtual network on AWS. The following services and features are also important:
- Amazon VPC Security Groups provide a per-host stateful firewall, allowing you to specify traffic rules and define relationships to other security groups.
- AWS Shield is a managed distributed denial of service (DDoS) protection service that safeguards web applications running on AWS.
- AWS WAF is a web application firewall that helps protect your web applications from common web exploits that could affect application availability, compromise security, or consume excessive resources.
- AWS Firewall Manager is a security management service that makes it easier to centrally configure and manage AWS WAF rules across your accounts and applications.
- AWS Direct Connect allows you the ability to establish your own direct connectivity from your data center to your VPC.
System Security Configuration and Maintenance
The key AWS features that support the protection of your systems is AWS Systems Manager. The following services and features are also important:
- Amazon Inspector can be used to identify vulnerabilities or deviations from best practices in your guest operating systems and applications.
- AWS CloudFormation can be used to create and manage infrastructure.
Enforcing Service-Level Protection
The key AWS service that supports service-level protection is IAM, which lets you define specific policies for many AWS resources. The following services are also important:
- AWS KMS allows you to set policies on the individual key.
- Amazon S3 allows you to set bucket policies for each S3 bucket.
- Amazon Simple Notification Service (Amazon SNS) topics allows you to set a policy statement on each topic
Encryption/Tokenization
The key AWS service that supports encryption is AWS KMS, which provides an easy-to-use, secure, and redundant key management service. The following services are also important:
- AWS CloudHSM provides a hardware security module for managing your keys
- Amazon DynamoDB provides a way to implement a fast NoSQL database. This can be used to store encrypted content for your tokens.
Protecting Data at Rest
The key AWS service that protects data at rest is AWS KMS, which is a managed service that makes it easy for you to create and control encryption keys. The following services are also important:
- Amazon S3 is an object storage service that integrates with AWS KMS, and allows you to supply your own keys.
- Amazon EBS is a block storage service integrated with AWS KMS. You can also perform block-level encryption with your operating system tools or third-party solutions.
- Amazon Glacier is a secure, durable, and extremely low-cost storage service for data archiving and long-term backup that encrypts data at rest.
Protecting Data in Transit
The key AWS service that protects data in transit is ACM, which helps you generate certificates used for establishing encrypted transport between systems. The following services and features are also important:
- Elastic Load Balancing supports secure protocols including HTTPS with ACM integration.
- Amazon CloudFront supports encrypted endpoints for your content distributions.
Data Backup/Replication/Recovery
The key AWS service that supports data backup, replication, and recovery is Amazon S3. The following services and features are also important for backup and replication of data:
- Amazon S3 Cross-Region Replication is an Amazon S3 bucket-level feature that enables automatic, asynchronous copying of objects across buckets in different AWS Regions.
- Amazon S3 lifecycle polices and versioning allow you to implement a backup strategy and meet retention requirements.
- Amazon EBS snapshot operations let you back up your volumes attached to EC2 instances.
Incident Response
Even with extremely mature preventive and detective controls, your organization should still put processes in place to respond to and mitigate the potential impact of security incidents. The architecture of your workload strongly affects the ability of your teams to operate effectively during an incident, to isolate or contain systems, and to restore operations to a known good state
Several key AWS services and features are critical to a mature incident response process:
- IAM should be used to grant appropriate authorization to incident response teams in advance.
- AWS CloudFormation to automate the creation of trusted environments for conducting deeper investigations.
- AWS CloudTrail provides a history of AWS API calls that can assist in response, and trigger automated detection and response systems.
- Amazon CloudWatch Events to trigger different automated actions from changes in AWS resources including CloudTrail.
- AWS Step Functions to coordinate a sequence of steps to automate an incident response process.
References:
- https://docs.aws.amazon.com/cognito/latest/developerguide/authentication-flow.html
- https://www.reddit.com/r/devops/comments/au5ao2/aws_cross_account_and_federation_help/
- https://aws.amazon.com/pt/answers/account-management/aws-multi-account-billing-strategy/
- https://d1.awsstatic.com/whitepapers/aws-security-best-practices.pdf
- https://d1.awsstatic.com/aws-answers/AWS_Multi_Account_Security_Strategy.pdf
- https://d1.awsstatic.com/whitepapers/Security/DDoS_White_Paper.pdf
- https://d1.awsstatic.com/whitepapers/Security/AWS_Security_Whitepaper.pdf
- https://d1.awsstatic.com/whitepapers/architecture/AWS-Security-Pillar.pdf










Nenhum comentário:
Postar um comentário
Observação: somente um membro deste blog pode postar um comentário.